TanStack NPM Compromise: Supply-Chain Trust Is Broken
A supply-chain attack hit the TanStack NPM ecosystem — here's what builders need to know about trusting open-source dependencies.
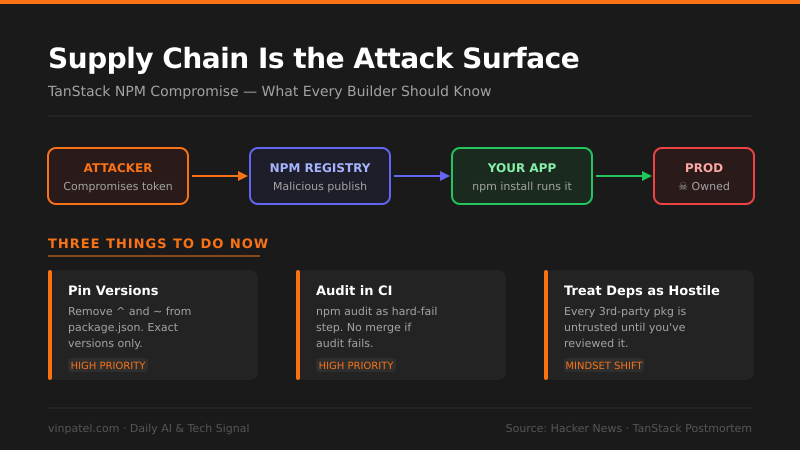
The signal: TanStack, one of the most trusted headless UI/data libraries in the JS ecosystem, published a postmortem on an NPM supply-chain compromise that snuck malicious code through its package distribution.
Why it matters: If a widely-used, well-maintained library like TanStack can get hit, your dependency tree is not safe by default — full stop. Every package you pull in without pinning, auditing, or verifying is a potential backdoor into your production environment.
The pattern I’m watching: Supply-chain attacks are becoming the preferred vector precisely because developers have gotten good at defending their own code — so attackers moved upstream. AI-assisted coding is making this worse: AI tools confidently suggest npm install without any security context, and developers ship faster than they audit.
What I’d do with this: Lock your dependency versions today — no more ^ or ~ in package.json for critical libraries — and add npm audit as a hard-fail step in your CI pipeline. If you’re building anything with user data, treat every third-party package as hostile until proven otherwise.
Get the daily signal in your inbox